Article Summary
The buzz around exploitation in WordPress plugins was not yet down, when a new report of exploitation in WordPress theme Yellow Pencil Visual theme customizer surfaced. This theme was quite popular with more than 30000 active installations at the time it was taken down from the WordPress’s official site. After the vulnerabilities in two of its software was made public by a security researcher, the attempts of exploitation soared. Due to the attacks that followed many sites are now redirecting to other malicious sites
The buzz around exploitation in WordPress plugin Yuzo Related Posts was not yet down when a new report of exploitation in WordPress plugin Yellow Pencil Visual Theme Customizer surfaced. This plugin was quite popular with more than 30,000 active installations at the time it was taken down from WordPress’s official site. After the vulnerabilities in two of its software were made public by a security researcher, the attempts of exploitation soared. Due to the attacks that followed many sites are now redirecting to other malicious sites
Current Status of The Yellow Pencil Exploitation
I tried finding Yellow Pencil Visual Theme Customizer on WordPress and this result came:
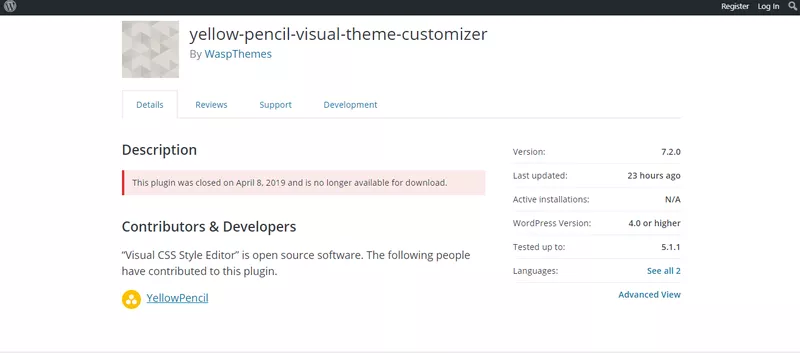
Even though the description clearly shows it was last updated only 23 hours ago i.e. on 12th of April and a new version 7.2.0 has been made live, Still, WordPress has taken the plugin off its page due to the frequency of the attacks. Further, the current users of the Yellow Pencil Visual Theme Customizer are being advised to uninstall it without delay to stop the attack from reaching their WordPress websites.
Related Article: WordPress Admin Panel Hack
Vulnerabilities in Yellow Pencil Plugin Exploitation
The two vulnerabilities that made to the limelight after these were made public on a blog with a PoC (proof of concept) are listed below.
WordPress website redirects & unknown users added? Visit Astra or Drop a message on the chat widget, and we will be happy to help you. Fix your Hacked WordPress website now.
Privilege-Escalation Vulnerability
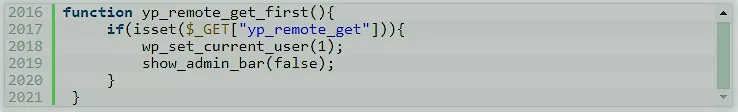
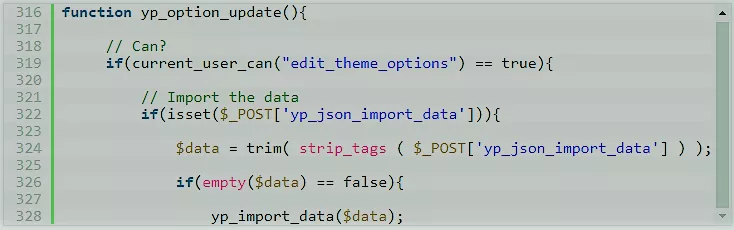
The first vulnerability which is being exploited in this plugin is the “Privilege-escalation vulnerability”. It has arisen due to a flaw in the yellow-pencil.php file in the plugin. In the yellow-pencil.php a function yp_remote_get_first( ) is set, which checks requests coming from the (yp_remote_get) function. Due to this, unauthenticated users get access to the powers an admin possess.
Cross-Site Request Forgery (CSRF) Check
The second vulnerability is not due to the presence of a specific function instead it is due to the absence of A Cross-site request forgery (CSRF) check, which would have put an extra barrier to these coming attacks. Not having CSRF check allows an unauthenticated user to exploit this bug.
Moreover, it is also known that all the recent attacks such as Yuzo Related Posts Plugin, social warfare, etc are executed by the same IP address. It is conjectured that a security researcher at odds with WordPress is behind the serial attacks.
Related Guide – WordPress Malware Removal
Conclusion- Yellow Pencil Plugin Exploitation
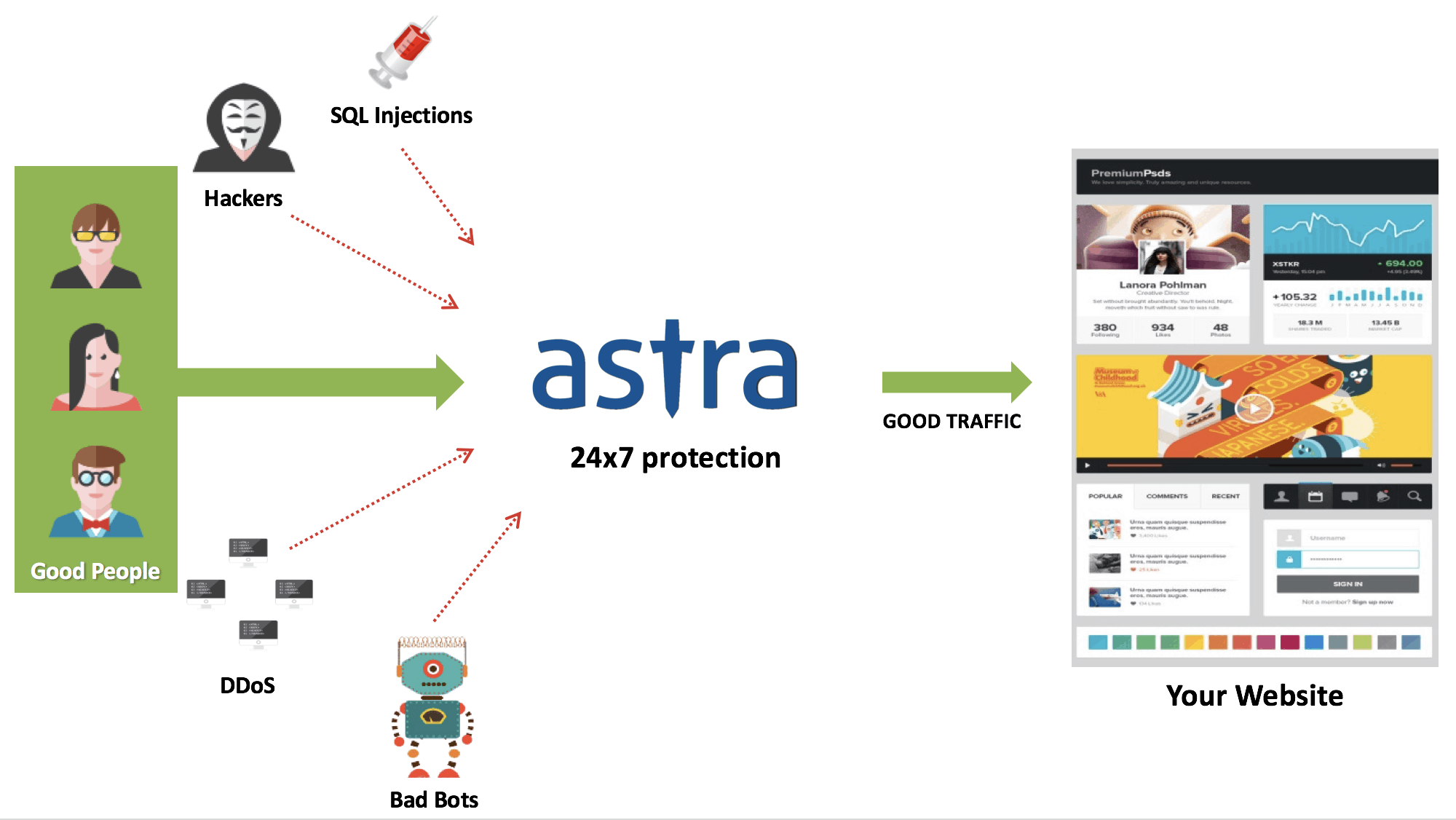
As we have seen in recent cases, uninstalling, updating, and resetting is the cure. Besides, having a firewall like Astra’s Firewall for WordPress on your website will sure do a lot for your website’s security & zero-day attacks. Astra Website Security Suite is an all in one security solution for a website. Our Malware Scanner scans and mends your website in a jiffy of time.